In the ever-evolving landscape of cybersecurity, one question looms large: what cyber attack is the hardest to prevent? As technology advances and cyber threats become increasingly sophisticated, identifying the most elusive and challenging attacks to defend against is crucial for organizations and individuals alike. Let’s delve into this complex issue and uncover the enigmatic nature of cyber attacks.
The Hydra of Cyber Threats: Understanding Complexity
Cyber attacks come in many forms, each with its own set of tactics, techniques, and procedures (TTPs). From malware and phishing to DDoS (Distributed Denial of Service) attacks and insider threats, the arsenal of cybercriminals is vast and diverse. However, amidst this myriad of threats, certain attacks stand out for their elusive nature and ability to circumvent traditional security measures.
Advanced Persistent Threats (APTs): The Stealthy Adversary
At the forefront of elusive cyber attacks are Advanced Persistent Threats (APTs). Unlike opportunistic attacks that target vulnerabilities indiscriminately, APTs are highly targeted and meticulously planned campaigns orchestrated by skilled adversaries, often with significant resources at their disposal.
APTs are characterized by their stealthy and persistent nature. These attackers employ sophisticated tactics to infiltrate networks, evade detection, and maintain long-term access to sensitive information. By leveraging techniques such as social engineering, zero-day exploits, and custom malware, APT actors can bypass traditional security controls and remain undetected for extended periods.
Zero-Day Exploits: The Vulnerability Dilemma
Zero-day exploits pose another significant challenge for cybersecurity defenders. These exploits target previously unknown vulnerabilities in software or hardware, giving attackers the upper hand by exploiting weaknesses that have not yet been patched or mitigated.
Zero-day exploits are particularly difficult to prevent because defenders have little to no advance warning or defense mechanisms in place. Once a zero-day vulnerability is discovered and exploited, it can have far-reaching consequences, potentially compromising entire systems or networks before a patch is developed and deployed.
Insider Threats: The Trojan Horse Within
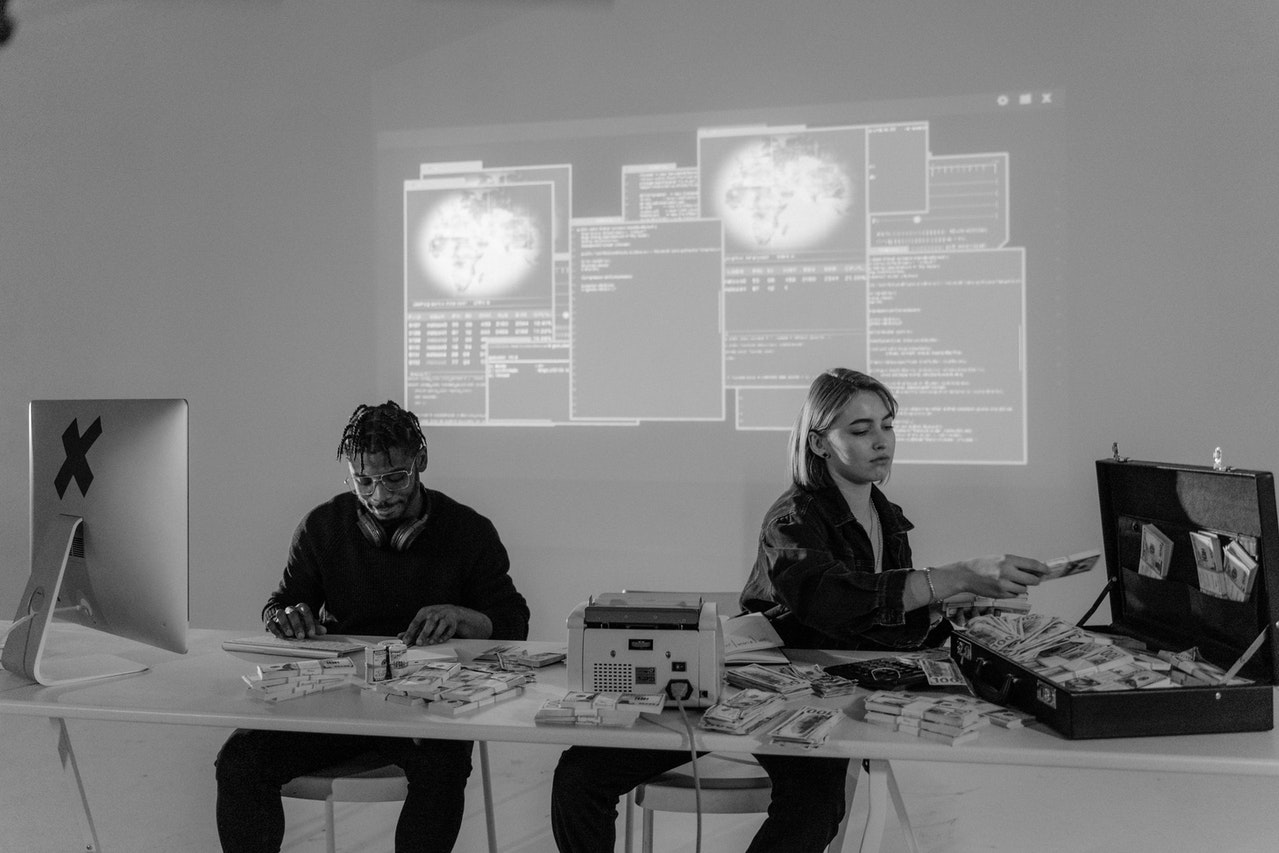
While external threats often dominate headlines, insider threats pose a significant risk to organizations’ cybersecurity posture. Whether intentional or unintentional, insiders with privileged access to sensitive data can inflict substantial damage by abusing their privileges or falling victim to social engineering tactics.
Detecting and mitigating insider threats is challenging due to the inherent trust placed in employees and the difficulty of distinguishing between legitimate and malicious behavior. Insider threats can take many forms, including data exfiltration, sabotage, and espionage, making them notoriously difficult to prevent and mitigate.
The Road Ahead: Strengthening Cyber Resilience
As cyber attacks continue to evolve in sophistication and scale, organizations must adopt a proactive approach to cybersecurity. This includes implementing robust security measures, conducting regular risk assessments, and investing in employee training and awareness programs.
Additionally, leveraging advanced technologies such as artificial intelligence (AI), machine learning (ML), and threat intelligence can enhance organizations’ ability to detect and respond to emerging threats in real-time.
Ultimately, while certain cyber attacks may be more challenging to prevent than others, proactive defense strategies and a culture of cybersecurity awareness can help organizations stay one step ahead of adversaries and mitigate the impact of even the most elusive threats.
In conclusion, the question of what cyber attack is the hardest to prevent is multifaceted and dynamic, reflecting the constantly evolving nature of the cybersecurity landscape. By understanding the tactics and techniques employed by adversaries and implementing effective defense strategies, organizations can bolster their resilience and protect against a wide range of cyber threats.